I’ve noticed something concerning lately – some folks are using their wallets without any crypto wallet security practices to safeguard their money.
It’s worrying, especially considering the numerous hacks where innocent users lost heaps of their hard-earned cash.
Take the case of billionaire investor Mark Cuban, who lost a staggering $870,000 in September 2023 when his MetaMask wallet was compromised.
A lot of these incidents could have been avoided if people followed some basic security practices for their crypto wallets.
You definitely don’t want to be the next victim, especially with these sneaky hackers and scammers out there eyeing your crypto funds.
To help you out, I’ve put together a list of 7 crypto wallet security best practices to keep your crypto wallet safe and sound.
Let’s make sure your funds stay where they belong – in your wallet!
Understanding the Basics
Cryptocurrency might seem all futuristic, but really, it’s just a clever and modern idea.
Picture a wallet, not filled with cash and credit cards, but instead a digital safe for your virtual currencies like Bitcoin, Ethereum, and others.
This digital wallet, often called a crypto wallet, is your doorway into the world of decentralized finance.
In simple words, a crypto wallet is like your online bank account. It stores your cryptocurrencies and facilitates transactions.
But, there’s more to it than that.
Types of Crypto Wallets: Hot vs. Cold
Crypto wallets come in two main types: hot wallets and cold wallets.
- Hot Wallets (Online): These are wallets that are connected to the internet, so you can use them on different devices. Hot wallets are convenient for everyday buying and selling, but they are more at risk from online dangers.
- Cold Wallets (Offline): Cold wallets are a bit like your savings account. They’re not connected to the internet when you’re not using them, which makes them extra safe. Hardware wallets and paper wallets are common types of cold wallets.
Deciding between a hot and cold wallet depends on your usage.
Hot wallets are like your everyday wallet, good for small amounts and regular spending. Cold wallets, though, are like a super secure vault for keeping larger amounts safe.
Read Also: Everything You Should Know About Crypto Wallet
Risks Associated with Inadequate Crypto Wallet Security
Now that we’ve got the basics of crypto wallets down, it’s time to talk about something important: the risks associated with inadequate crypto wallet security measures.
Crypto is cool, but there are some real dangers if you don’t take security seriously.
1. Unauthorized Access:
- Risk: Without robust security measures, unauthorized individuals may gain access to your wallet.
- Consequence: Loss of funds or theft of your cryptocurrencies.
2. Phishing Attacks:
- Risk: Malicious attempts to trick you into revealing sensitive information, such as login credentials or private keys.
- Consequence: Unauthorized access to your wallet and potential loss of funds.
3. Lack of Backup:
- Risk: Failure to create backups of your crypto wallet information.
- Consequence: Permanent loss of access to your cryptocurrencies if your device is lost, damaged, or compromised.
Read Also: How to Backup Your Crypto Wallet
4. Outdated Software:
- Risk: Neglecting to update your wallet software.
- Consequence: Vulnerability to security exploits that have been patched in newer versions.
5. Public Wi-Fi Vulnerabilities:
- Risk: Conducting crypto transactions over unsecured public Wi-Fi networks.
- Consequence: Exposure to potential man-in-the-middle attacks, leading to unauthorized access.
6. Neglecting Two-Factor Authentication (2FA):
- Risk: Failure to enable 2FA on your wallet.
- Consequence: Increased susceptibility to unauthorized access, especially if passwords are compromised.
Knowing about these risks is the first step to keeping your crypto wallet safe.
Now, let’s look at some crypto wallet security best practices to protect your cryptocurrencies from these potential threats.
7 Best Practices for Crypto Wallet Security
Now that we know about the possible dangers, let’s explore the top crypto wallet security best practices to keep your wallet safe.
1. Regularly Update Your Wallet Software
Just like a well-maintained car makes your journey smooth, it’s important to keep your crypto wallet software updated for a safe and hassle-free experience.
Here’s why regular updates are a big deal:
- Security Updates: When developers release updates, they often include important security fixes. Think of them as repairs to potential weak spots in your wallet’s armor. Updating protects your wallet from sneaky attempts by hackers to exploit vulnerabilities.
- Enhanced Features: Updates aren’t just about security. They can also bring in nifty new features and tweaks that make your wallet even better. It’s like getting a free upgrade that not only makes things easier but also adds extra layers of protection.
- Compatibility: The crypto world moves fast, and the technology behind it is always evolving. Regular updates ensure your wallet remains compatible with the latest changes in the crypto world. This means your transactions keep ticking smoothly without any hiccups.
By making sure your crypto wallet software is up to date, you’re basically giving it a suit of digital armor against potential security threats.
So, it’s worth taking a few moments to hit that update button!
2. Be Cautious with Public Wi-Fi
Using free Wi-Fi might seem handy, but it comes with risks you need to know about.
Here’s why Public Wi-Fi can be risky:
- Unencrypted Connections: Public Wi-Fi networks often lack encryption, leaving your data vulnerable to interception by cybercriminals lurking on the same network.
- Man-in-the-Middle Attacks: Cyber attackers can employ sophisticated techniques to intercept communication between your device and the network, potentially gaining access to sensitive information such as passwords or private keys.
- Rogue Hotspots: Hackers can set up fake Wi-Fi hotspots with names similar to legitimate ones, tricking users into connecting to them. Once connected, all data transmitted can be compromised.
- Packet Sniffing: Tools exist that allow hackers to capture and analyze data transmitted over public Wi-Fi networks. This can include login credentials and other sensitive information.
Read Also: 4 Best VPNs For Crypto Trading
3. Be Wary of Phishing Attempts
Phishing is a deceptive trick used by online crooks to fool people into giving away important info like usernames, passwords, or, in crypto, private keys.
They often pretend to be trustworthy sources, pulling victims into doing stuff that could cause harm.
How to Spot and Avoid Phishing Attempts:
- Verify Website URLs: Before typing in your login stuff or private keys, take a good look at the website’s URL. Scammers love making fake websites that look real. Watch out for tiny misspellings or variations in the URL.
- Look for the Padlock and “https”: Real websites, especially the ones handling sensitive information, use “https://” in their address. Also, keep an eye out for a little padlock symbol in the address bar. It’s a good sign.
- Be Skeptical of Unsolicited Emails: Phishing attempts often come via unsolicited emails claiming urgent actions or requesting sensitive information. Be cautious, and verify the legitimacy of such communications independently.
- Inspect the Sender’s Email: Take a good look at the email address of the sender. Scammers might use addresses that appear similar to legitimate ones. Look for irregularities or misspellings.
- Verify Official Communications: If you’re not sure about a message, don’t trust it blindly. Independently check if it’s legit. Get in touch with the company or person using info from their official website, not the one in the suspicious message.
4. Enable Two-Factor Authentication (2FA)
Imagine having not just one, but two locks on the entrance to your fortress.
That’s the essence of 2FA.
It adds an additional layer of security beyond your standard password, making it significantly more challenging for unauthorized individuals to access your crypto wallet.
Why 2FA Matters:
- Enhanced Security: Even if someone somehow gets hold of your password, they’re still stuck. They need the second factor (usually a code sent to your phone) to actually gain access. So, it’s like having a backup lock – pretty handy, right? Especially if your password ever gets into the wrong hands.
- Reduces Phishing Risks: 2FA acts as a formidable defense against phishing attempts. Even if you accidentally share your password, those bad guys trying to trick you (phishers) hit a wall when they don’t have that second authentication factor to prove it’s really you.
- Protects Against Keyloggers: There are these sneaky programs called keyloggers that spy on what you type. But with 2FA, they’re rendered ineffective. Even if they grab your password, they’re missing the second factor required to get in.
So, when you turn on Two-Factor Authentication, you’re basically slapping an extra layer of security on your crypto wallet.
5. Keep Seed Phrase and Private Keys Safe
Keeping your seed phrase and private keys safe is paramount in ensuring the security of your crypto holdings.
These critical pieces of information grant access to your funds and must be safeguarded against unauthorized access and loss.
Here’s how you can keep your seed phrase and private keys safe:
- Understand the Importance:: Your seed phrase and private keys are the keys to your crypto kingdom. Anyone with access to them can control your funds. Treat them with the utmost care and diligence to prevent unauthorized access or loss.
- Store Offline in a Secure Location: Write down your seed phrase and private keys on a piece of paper or a physical medium. Store them in a secure, offline location such as a safe, lockbox, or hidden compartment. Avoid storing them digitally, as digital storage can be vulnerable to hacking and malware.
- Keep Multiple Copies: Create multiple copies of your seed phrase and private keys. Store copies in separate secure locations to reduce the risk of loss due to fire, theft, or natural disasters.
- Don’t Share Your Seed Phrase or Private Keys: Never share your seed phrase or private keys with anyone, including friends, family, or support staff. Legitimate entities will never ask you to provide your seed phrase or private keys.
Your seed phrase and private keys are also essential for wallet recovery in the event of loss, theft, or damage to your primary wallet.
They enable you to regain access to your funds and restore your wallet’s functionality.
So, keeping them safe isn’t just a good idea – it’s essential for protecting your cryptocurrencies!
6. Test Wallet Recovery Procedures
In the crypto market, preparation is the anchor that keeps your investments secure amidst turbulent times.
Why Testing Wallet Recovery Procedures Matters:
- Preventing Loss of Funds: Testing your wallet recovery process helps make sure you don’t lose your crypto if something unexpected happens, like your computer breaking, losing your login details, or if there’s a problem with the software.
- Ensuring Readiness for Emergencies: Practicing wallet recovery procedures prepares you to respond effectively to emergencies, minimizing downtime and financial losses.
- Making Sure Your Backups Work: Testing your wallet recovery process helps you make sure that your backup files are good to go. You want to be certain they have all the right information to restore access to your funds if you need it.
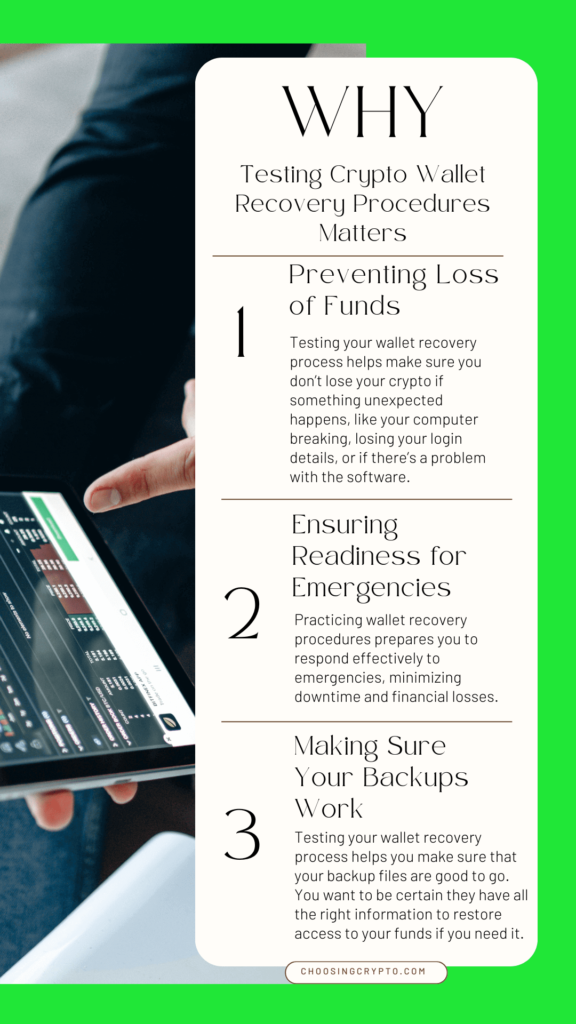
Remember, it’s like having a spare key to your house – you hope you never need it, but you’ll be glad you have it if you do!
7. Use Burner Wallets for Airdrops
Airdrops present lucrative opportunities for crypto enthusiasts to receive free tokens.
But they can be risky as some airdrops may require connecting your addresses with unsafe websites.
Why Use Burner Wallets for Airdrops Matters:
- Isolation from Primary Holdings: Burner wallets provide a temporary and isolated space for claiming airdrops. This isolation ensures that your primary wallet, containing large holdings, remains secure and unaffected by the airdrop process.
- Enhanced Privacy: Using burner wallets contributes to enhanced privacy by preventing airdrop activities from being directly linked to your primary wallet. This reduces the risk of potential targeted attacks or phishing attempts based on airdrop participation.
- Reduced Exposure to Scams: Burner wallets help reduce the risk of scams associated with airdrops. Since these wallets are disposable and separate from your main holdings, any potential scams or vulnerabilities are contained within the temporary environment.
So, if the worst happens and someone manages to hack into your burner wallet, it’s not the end of the world.
Your main crypto wallet stays safe, away from harm’s reach.
Read Also: What Airdrop Mean in Crypto Market and How it Works
Conclusion
To sum it up, safeguarding your crypto assets isn’t just a choice – it’s a responsibility.
The worrying stories of hacked crypto wallets and people losing a lot of money highlight how crucial it is to follow good security practices.
By putting into practice the crypto wallet security practices that we talked about earlier, you’re not just keeping your money safe. You’re taking charge of your financial safety.
Let’s be strong against the sneaky threats from hackers and scammers.
Your crypto funds should be in your wallet, and with the right practices, that’s exactly where it’ll stay.
Additional Resources
Excited to learn more about Bitcoin and cryptocurrencies? We’ve got some awesome resources below to help you out.
Additional Resources:
- 7 Best Ways to Secure Your Cryptocurrencies
- The Difference Between A Crypto Wallet and Exchange
- Best Crypto Hardware Wallets for Storing Crypto Offline
- 5 Best Crypto Mobile Wallets
- Most Common Crypto Scams and How to Avoid Them
- Crypto Hot Wallet vs Cold Wallet
- 20 Things You Should Never Do as a Crypto Investor/Trader
- How to Report Crypto Scam
And guess what? We’re also on Instagram and Twitter(X). Join us there for even more fun and useful content!

DISCLAIMER:
The information provided here is intended for informational purposes only and should not be solely relied upon for making investment decisions. It does not constitute financial, tax, legal, or accounting advice. Additionally, I strongly recommend that you only invest in cryptocurrency an amount you are comfortable with potentially losing temporarily.
Read Also: How to Transfer Crypto to Hardware Wallet
